Burp
This plugin is a script developed in Java as a extender to the Burp Proxy API (Pro/Community).
Installation¶
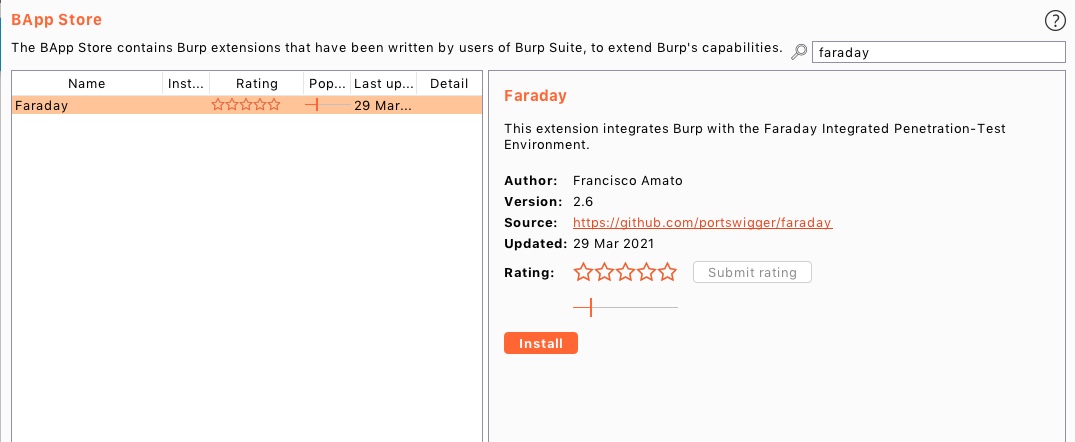
From the App Store¶
You can install the Burp extension from the Burp App Store
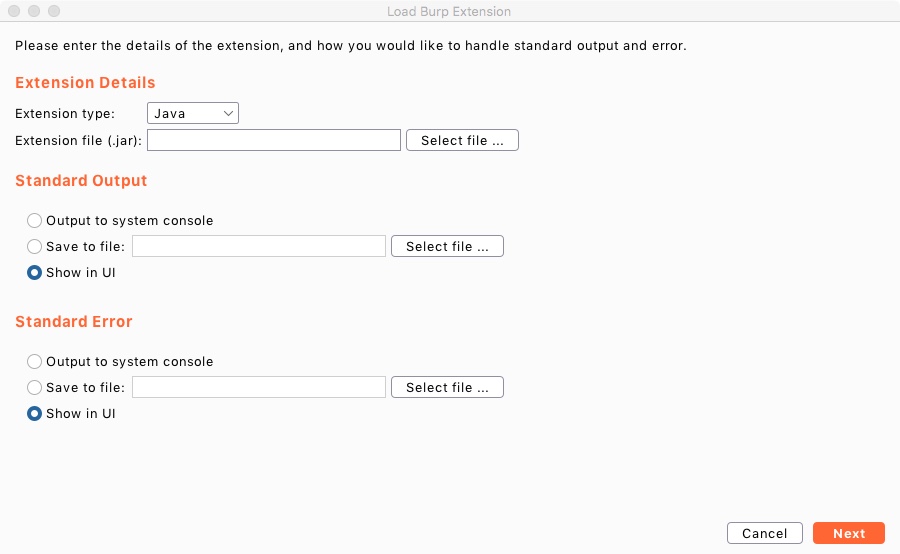
From file¶
Download the jar from this link
Once you have it, follow these steps:
-
Go to Extender->Extensions and click in the Add button.
-
In the Extension Details section, the extension type should be Java, and select the file.
-
Click Next, and if everything went well, you should see no errors and you can close the window.
-
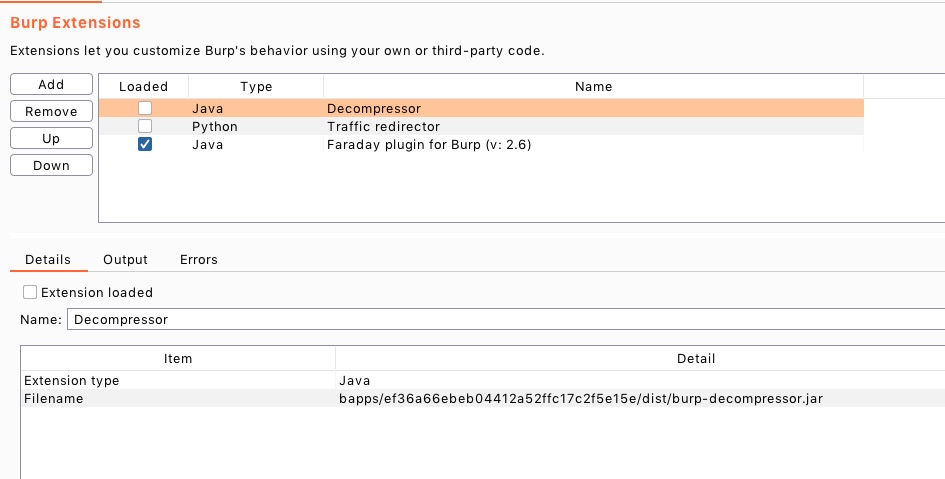
Now, make sure the extension is loaded in the Extensions tab.
Extension configuration¶
Once the Faraday extension is loaded into your Burp, you will see a new tab called "Faraday".
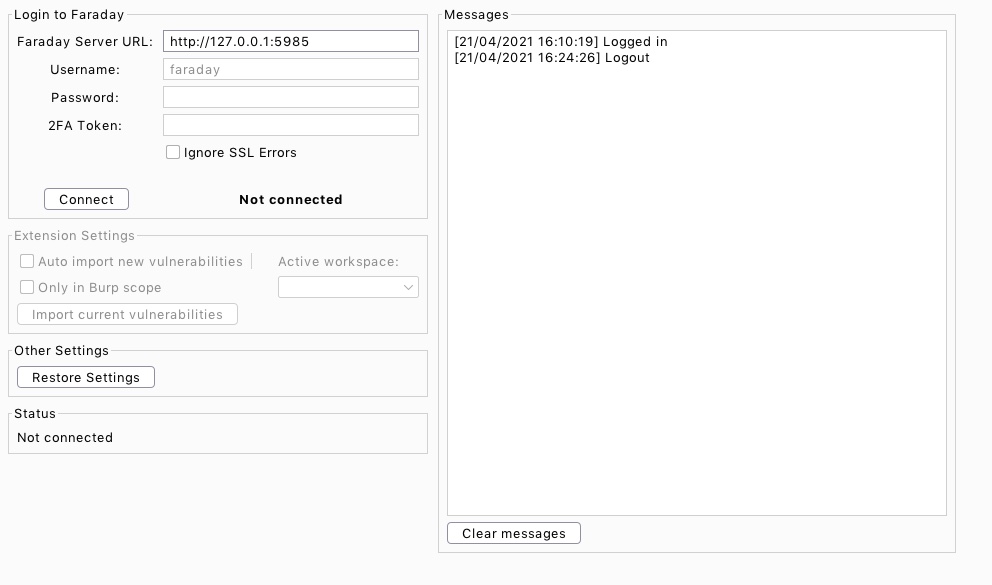
Here, you can login to Faraday and you can edit the extension's settings:.
Login to Faraday¶
In order to connect the Faraday's Burp extension to Faraday, follow these steps:
1) Set your Faraday Server URL. This should point to the same URL that you use when you are connecting to Faraday Server, e.g: http://127.0.0.1:5985
2) Connect Burp to Faraday by clicking on the Connect button.
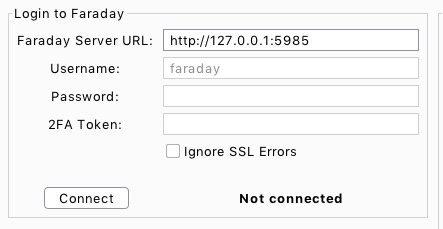
3) Once you are connected, type your Faraday's credentials: username, password and 2FA Token (if it is the case).
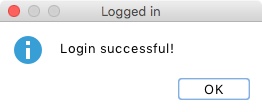
4) Login into Faraday by click on the Login button. If everything goes well, Burp should pop up a Login successful! modal.
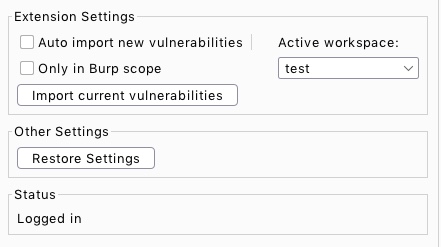
5) Once you are logged in, you can edit the extension's settings.
Extension Settings¶
From here, you can:
1) Choose the workspace where you want to work on.
2) Choose whether the vulnerabilities should be imported automatically or not (it's disabled by default).
3) Import the vulnerabilities you've found so far.
4) Check if you want to use only Burp scope.
Send to Faraday¶
Once you have everything setup, you can send the issues or requests to Faraday.
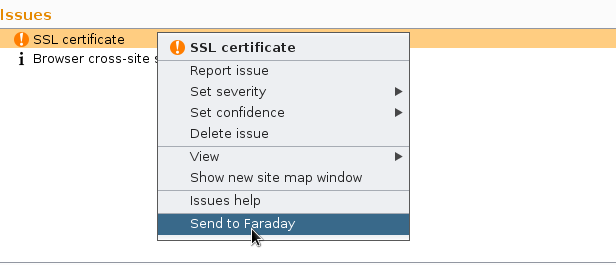
!!! warning "REMEMBER: If the request is missing the response, the information can't be sent to faraday! REMEMBER 2: Vulnerabilities will only work with commercial versions of burp"
Other Settings¶
From here, you can Restore Settings to default.