Tasks
You can create your own custom Methodologies, add Tasks, tag them and keep track of your whole project directly from Faraday.
Faraday comes with Methodologies loaded by default that allow you to get to work quickly without having to create your own.
A few of our default Methodologies:
PCI DSS 11.2 Hardware Top 10 Mobile Security Network Pentest Owasp Top 10 Loading a default Methodology All default Methodology files are available at the bottom of this page. Download them, then use the "New" button and select the option "From template", give this new methodology a name and that's it!
You can download the methodologies at the bottom of this article.

Creating you own Methodology¶
Create a .csv file with the following fields:
name description Then, use the "Import" button and select your new .csv to load your custom Methodology to Faraday.
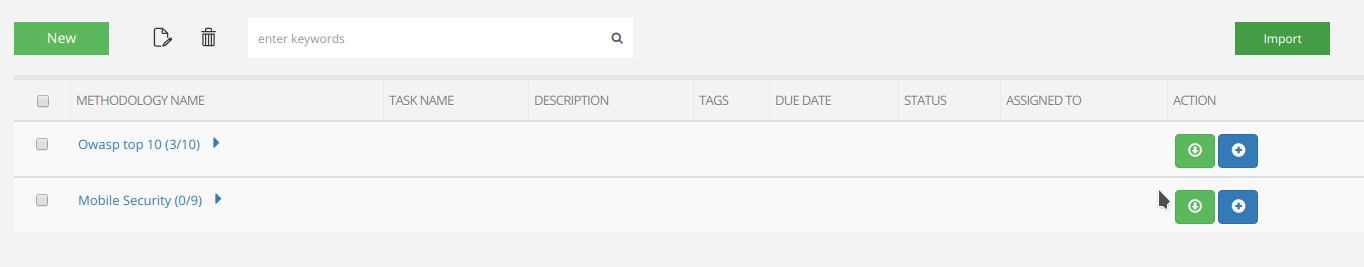
Downloading your preferred Methodology¶
Do you have a custom Methodology created from scratch? Click in "Download CSV for current Methodology" and you will download a .csv file with the information for it!
Kanban View¶
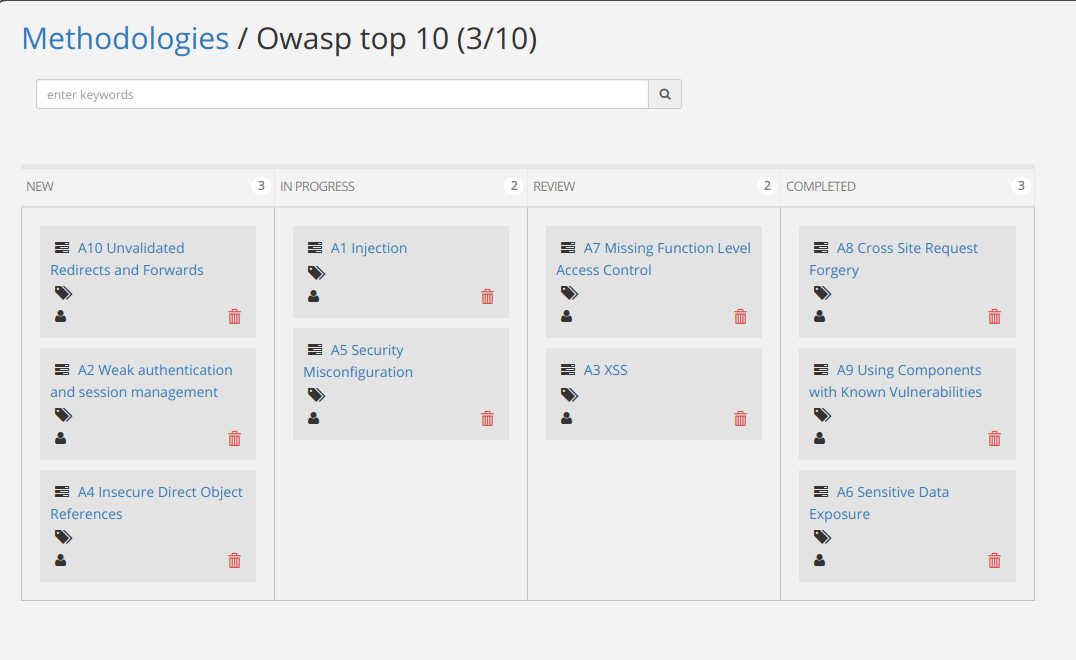
If you click on the Methodology name, you'll access the Kanban view for it.
You can use drag and drop to change the status of the different Tasks, or you can create a new one. You can also edit or delete a task.
Task¶
Methodologies contain Tasks, which include the following fields:
- Name
- Description
- Due date
- Status
- Users assigned
- Tags
With that, you can assign a specific Task with a due date to a pentester. Also, tag a chunk of Tasks for a better appreciation in the Kanban view.
![]()